WebInspect is definitely not a stealthy tool; and that’s fine, because you shouldn’t be secretly auditing anyone’s website. Here are a few of the signs that WebInspect leaves when doing a crawl and audit of a website.
WebInspect Scan Signature: The webinspect scan signature is a request that webinspect sends to the server with the text SCANNED-BY-SPI-DYNAMICS-WEBINSPECT-WWW.SPIDYNAMICS.COM. This will be found in the webserver logs, identifying that a scan has taken place.
In the web server logs, the request may look something like this…
127.0.0.1 - - [03/Feb/2008:18:44:08 +1000] "GET /----SCANNED-BY-HP-WEBINSPECT---- HTTP/1.1" 404 -1 "http://127.0.0.1:1080/" "Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 5.1; SV1; .NET CLR 1.1.4322)"
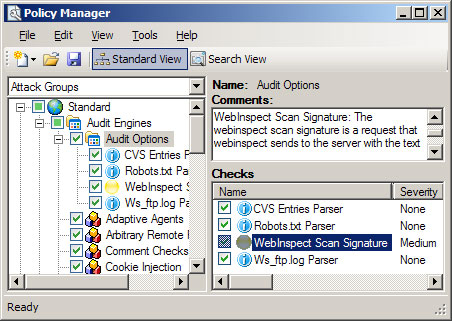
You can disable this feature by opening Policy Manager and unchecking Audit Options > WebInspect Scan Signature.
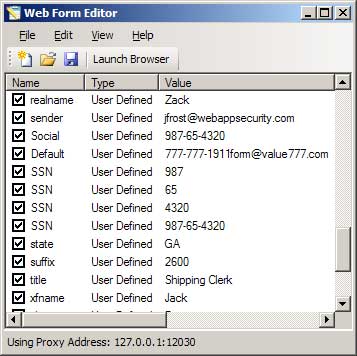
Posted Form Values: WebInspect will submit various values to any forms it encounters. One of these values is “777-777-1911form@value777.com” (87,500 Google results). The form values that WebInspect uses can be modified using the Web Form Editor program.
If you would like to run a crawl and audit without posting any form values (I can’t really see the point of doing this though), then you can uncheck Auto-fill web forms during crawl in the Scan Settings > Method window.
Attacks in web server logs: In addition to the WebInspect Scan Signature, WebInspect will leave plenty of evidence of its activities in the web server logs. A good example is a GET request for “/SPIfingerprint404chk”, which is used to try to identify the target’s web server based on the returned 404 error page. Any of these individual attacks can be disabled using the Policy Manager (not that you would want to do this).
One Comment
Comments are closed.



The goolge search for 777-777-1911form@value777.com now returns “about 101,000” results! Though only one when restricted to Australia.